Most people know and adore pups like these:
The not so cute PUPs are Potentially Unwanted Programs that may come preloaded on your brand new computers, or installed alongside of programs that you add later. Just how prevalent these PUPs are? For example, 62% of the top 50 download @download(dot)com website includes PUPs.
So, what are these PUPs why are they pushed to you? They can be anything, such as adware, browser toolbars, homepage hijackers, nagging scare-ware, etc.
Adware is pretty much self explanatory; it’ll monitor your internet access and pops up ads related to you activities. While the popup ad can be annoying, like during your power point presentation (ugh!), this puppy will also collects your personal information and sends it “home”.
Browser toolbars install themselves into your browser to make your internet “browsing easier”. In exchange, this puppy will collect and send your personal information “home”, may popup ads, or redirects your search results to its paying customers’ websites based on your internet activities.
The homepage hijacker changes your current home page and acts as the browser toolbar afterward.
Nagging scare-ware is the trial version of security software. This software promises to clean up and secure your computer. The trial version will allow scanning your system, presents a scary results, but it does not allow you to fix them until you actually purchase a licensed version. The scary results have nothing to do with the state of your computer, they are auto-generated by the software to entice you to purchase the program. This puppy may have any of the other puppies integrated that will install as well.
Ok… They are not breaking my computer, so what’s the harm?
Other than changing the behavior and performance of your computer, they also collects information about you. This information can be extensive and correlated to offline data to tailor the popup ads to you and redirect your search result based on this information. The collected information about you also sold/traded to data brokers.
Ok… But I have nothing to hide and they probably have everything about me anyway.
That’s seemingly a fair point, but… Your computer performance will degrade and your search result isn’t what you are looking for. Some people like popup ads and that’s fine, can’t argue with that. How you view your privacy is also a personal preference.
Except that data brokers want current information about the person, since that is what valuable for them. Old data is pretty much useless as far as popping up ads is concerned. They are more than willing to pay for it and that is the main reason why these PUPs exist. If you don’t mind being a product created by these PUPs, there’s one more thing you should consider.
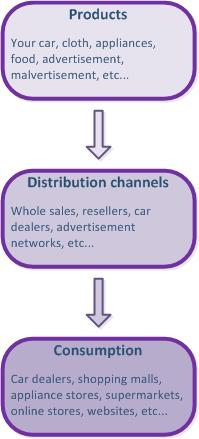
Malicious malware had started to utilize these PUPs to do their dirty work for them. They tie into these programs to collect your information, redirect your browser to download their malware and take over the control of your computer. Once they do, they will make you pay a ransom to have your computer back. You don’t have to believe me, just read this blog from Malwarebytes.
So, what can I do about these PUPs?
Prevention is the best proactive measure that you can take for PUPs free computer. Pay attention to the installation routine of the program that you want. Most of the PUPs are included as a recommended “additional program” that is selected by default to be installed. In most cases, you can deselect the recommended program and it won’t be installed. The more aggressive installation routines don’t allow you to deselect the PUP and some of them installs it hidden from you.
Ok, what do I do then?
Once you settled down and stopped swearing, my recommendation is installing programs that removes PUPs. There are two of them on my computers that used on a weekly basis:
No, they do not install PUPs, don’t be silly, and they are free…
Preferably, download and install both of them, update the engine if needed to, and run them one by one. While they are very good at removing PUPs, each software has its limitation. Just do it at least once and you’ll see how many PUPs you had on your computer. You can select to keep them, if you don’t mind the privacy and security risk that these PUPs pose to your computer, or delete them. You should also run these anti-malware programs on a weekly basis, if you want to have a PUPs free computer.