In the previous blog, we’ve looked at how malvertisement may affect you and what you can do to protect your system(s) against this threat vector. In today’s blog, we’ll look at the actual distribution channels and the cost for displaying malvertisement.
Beyond the advertisement shown in your browser, there’s a well established business model that isn’t that much different from any other business models.
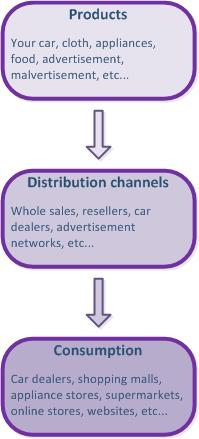 The picture on the left shows the typical business model. Basically the products are created (including malvertisement), sold to distributers, who in return make them available to consumers.
The picture on the left shows the typical business model. Basically the products are created (including malvertisement), sold to distributers, who in return make them available to consumers.
The difference is how other distribution channels are regulated and the requirements are enforced by various government agencies. You’d had hard time in the U.S. purchasing food at your supermarket, without FDA approval, buy a car without NHTSA approval, etc.
Unfortunately, the online advertisements are loosely regulated, with minimal, or no enforcement whatsoever. There’s no need for approval by the website or the advertisement network. They will pretty much blindly refer your browser to the site, where the actual ad is hosted. The actual site could be hacked websites, hosted servers, etc.
Hackers had discovered that they can just bid to display their ads at various sites. Since anyone can bid to display their ads, including the maximum price per displaying the ad, this is an easy way to have the malware distributed by reputable websites. The hackers’ malware incorporated in an ad (we call malvertisement), they bid to display their ad at targeted websites, and the advertiser network kicks in. When you visit the targeted websites, the ad becomes part of the website’s content, any script in the ad executed by your browser without you clicking on it. You probably recall a few websites that had some music and/or video already playing just by visiting their home page. This is the type of ad delivery that hackers use to load malware on to your system.
The process described is automated to the level that the chances are no humans evaluate the actual ad during this process. As such, malware is distributed without any warning. The sole exception might be your system protection that should stop the malware execution.
So, what is the actual cost for the hackers to display their ads? That depends on the website, where the ads are displayed. Malwarebytes blog states $0.927 per displayed ad with current malvertisement at the following websites:
- dailymotion.com
- theblaze.com
- nydailynews.com
- tagged.com
- webmail.earthlink.net
- mail.twc.com
- my.juno.com
Why neither the advertisement network, nor the websites are responsible for delivering malware in the ad, is beyond me. Holding the hackers responsible for the ad, but taking their money nonetheless, should be illegal.
Since your system protection should stop the malware, it raises a question. Why don’t the advertisement companies and websites test the ad for malware, prior to presenting it to the end users? It’s really not that hard to do:
- Advertiser receives the bid for the ad
- Client sends the ad to the advertiser
- Advertiser scans the ad for malware
- Advertiser approves the ad, if no malware found, and hosts it on their server
- Websites receive the ad from the advertiser, if they opt into their program
It’s harder to test the ad for malware by the website, but not impossible; real-time scanning for malware had been in existence for decades. The chances are that implementing such system would offset some or large part of the financial gains of displaying ads..
If security software on the client side can stop the malware, there should be no reason why advertisers and websites cannot scan the ad for malware. Samples of security programs that can stop 0-day malware:
There are certainly other security solutions that can stop 0-day malware, but antivirus isn’t one of them. The samples above are part of the security protection for my systems.
It’s unlikely that either the regulation or the advertisement distribution online will change anytime soon. There’s too much money to be made in the current ad delivery schema. As such, your favored website(s) might be serving up malware to your system that may just gobble them up. You should protect your system against them and by now, you should know that antivirus will not protect you.
Friends, don’t let friends rely on antivirus protection only…
